Securing Africa’s Digital Growth: Why Privileged Access Management Is Now Critical
As African enterprises accelerate digital transformation, one uncomfortable truth continues to surface:
Over 80% of cyber breaches still originate from weak or compromised credentials.
Despite significant investment in cybersecurity tools, attackers are not breaking in — they are logging in.
Across Africa, where organisations are rapidly adopting cloud, hybrid infrastructure, and distributed work models, identity has become the new security perimeter. And at the centre of this risk sits one of the most critical — and often overlooked — vulnerabilities:
Privileged access.
The Hidden Risk: Privileged Access as the Primary Attack Vector
Privileged accounts — administrative users, system accounts, service credentials — hold the keys to an organisation’s most critical systems.
They control:
- Core infrastructure
- Financial systems
- Customer data
- Cloud environments
- Operational platforms
It is no surprise then that privileged access remains one of the biggest attack vectors today.
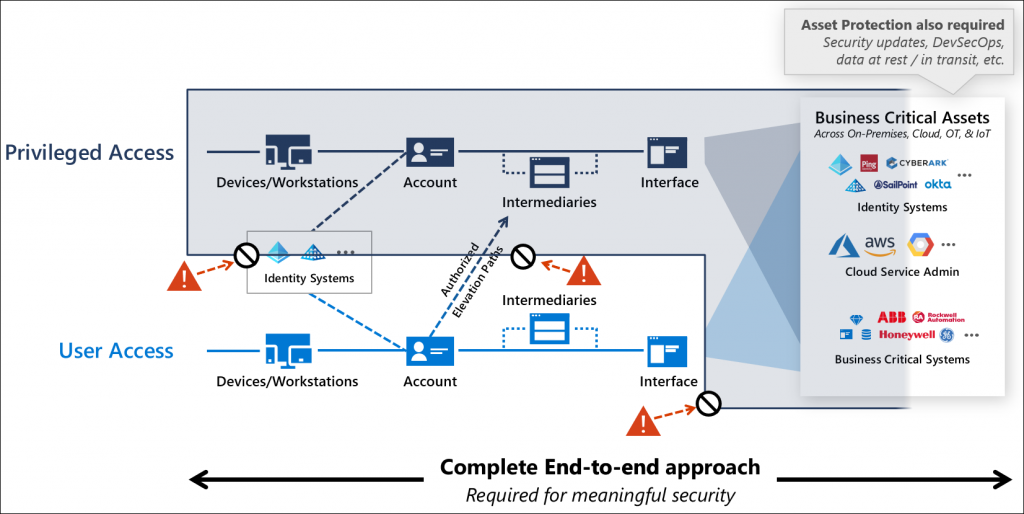
Yet many organisations are still relying on legacy tools or fragmented solutions that only address part of the problem — password vaulting without session control, endpoint tools without credential governance, or visibility without enforcement.
This creates dangerous gaps — and attackers know it.
The Problem with Legacy PAM Approaches
Traditional Privileged Access Management solutions were built for a different era — one where infrastructure was static, environments were centralised, and access was easier to control.
Today’s reality is very different:
- Hybrid and multi-cloud environments
- Remote access and distributed teams
- Increasing reliance on APIs, automation, and machine identities
- Growing compliance and audit requirements
In this environment, partial solutions are no longer enough.
Organisations need unified, identity-first security — not disconnected tools.
A Modern Approach: Enter KeeperPAM
Privileged access is still one of the biggest attack vectors—yet many organisations are relying on tools that only solve a small part of the problem.
That’s where KeeperPAM changes everything.
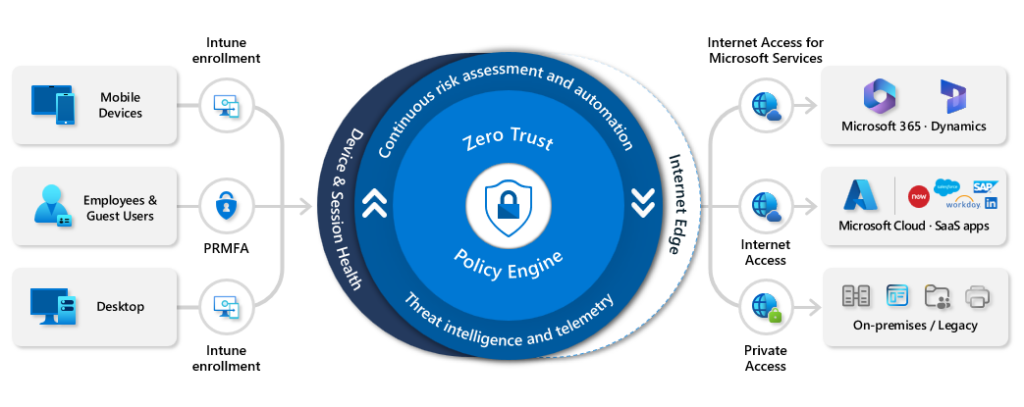
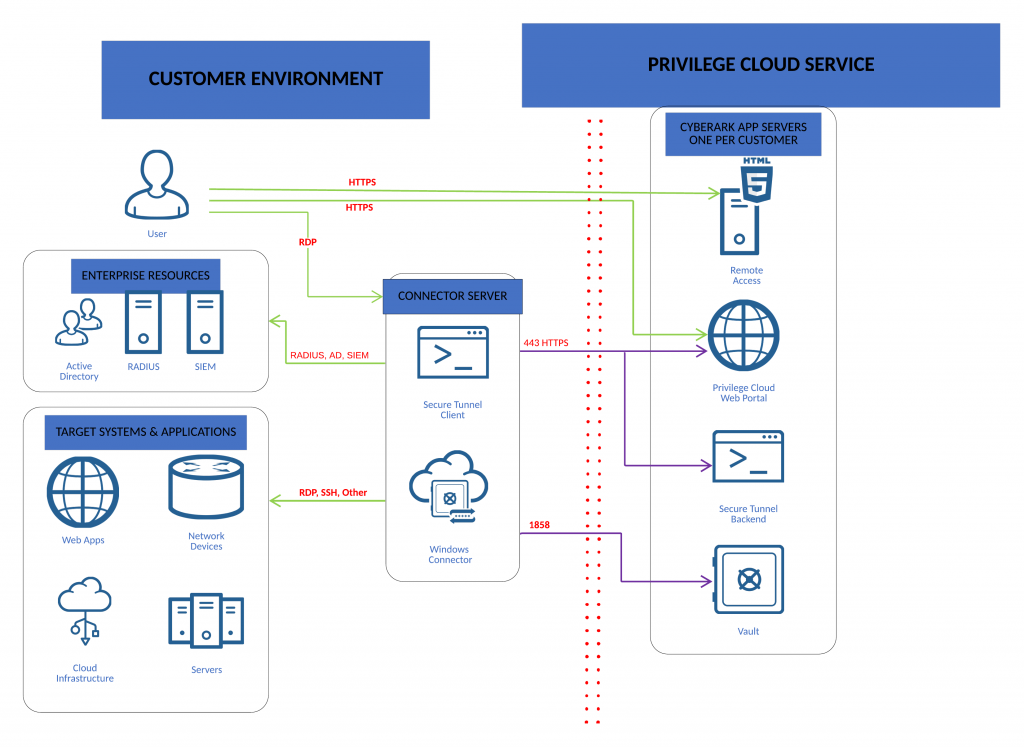
KeeperPAM is a modern, zero trust Privileged Access Management (PAM) platform that brings all your privileged controls into one secure, seamless experience. Designed for today’s hybrid environments, it protects your passwords, secrets, servers, cloud workloads, endpoints and remote sessions without adding complexity.
Why Organisations Are Moving to KeeperPAM
✔ Unified Security Platform
Consolidates credential vaulting, secrets management, remote session management, and endpoint privilege management into a single solution — eliminating tool sprawl.
✔ Zero Trust & Zero Knowledge Architecture
Every access request is verified, fully encrypted, and credentials are never exposed — even to the user.
✔ Just-in-Time (JIT) Access
Users gain time-limited access without ever handling credentials, with automatic rotation reducing long-term risk.
✔ Full Visibility & Auditability
Centralised oversight of all privileged accounts, sessions, and actions across on-prem and cloud environments.
✔ AI-Powered Threat Detection
Monitors and analyses privileged sessions in real time, helping organisations identify and respond to risky behaviour faster.
✔ Enterprise-Grade Compliance
Supports regulatory requirements including FedRAMP High, ISO 27001, SOC 2 Type II, HIPAA, and PCI DSS.
✔ Simplified Governance Across Environments
Streamlines privileged access control across servers, databases, applications, endpoints, and cloud workloads.
Why This Matters for African Enterprises
Africa’s digital economy is growing rapidly — but so are the threats that come with it.
Organisations across the continent face unique challenges:
- Skills shortages in cybersecurity
- Increasingly complex IT environments
- Rapid cloud adoption without consistent governance
- Budget constraints requiring efficient, consolidated solutions
In this context, identity security becomes the highest-impact investment.
Organisations that implement modern PAM and password management strategies can reduce breach risk by up to 70%.
At the same time, they gain:
- Operational resilience
- Improved compliance
- Greater visibility and control
- Confidence to scale securely
From Access Control to Business Resilience
Cybersecurity is no longer just a technical function — it is a business-critical priority.
Protecting privileged access is not about locking systems down.
It’s about enabling organisations to operate securely, scale confidently, and protect the trust of their customers and stakeholders.
At ATS Network Management, we are seeing a clear shift across the African market:
Enterprises that adopt modern, unified PAM platforms are moving from reactive security to proactive risk management.
Final Thought
Cybersecurity starts with controlling access.
In a landscape where attackers are targeting identities first, securing privileged access is no longer optional — it is foundational.
Africa’s digital future depends on getting this right.
Learn how your organisation can reduce risk and secure privileged access:
Engage with ATS Network Management to explore a modern PAM strategy tailored to your environment.






